The current era of DevOps has witnessed substantial progress..
Organisations can seamlessly deploy their workloads through the establishment of virtual machines. However, a critical aspect that is sometimes overlooked is security. The objective is to furnish self-service DevOps platforms, enabling developers to independently construct CI/CD pipelines and application monitoring dashboards. Many enterprises are making substantial investments in DevOps capabilities and endeavouring to devise a long-term deployment roadmap. Implementing DevOps services and solutions across the entire enterprises poses specific challenges, including:
Addressing security concerns Promoting DIY DevOps adoption Developing comprehensive CI/CD pipelines and monitoring strategies.
Revolux’s extensive expertise across diverse IT projects fortifies our capabilities in DevOps Engineering. Employing DevOps tools for automation and agile application lifecycle management, we have successfully executed over 20+ transitions. Our dedicated subject matter experts (SMEs) and research and development (R&D) teams leverage the Center of Excellence (CoE) at Revolux to craft forward-looking and future-proof IT solutions.
Devops Services
- Assesment & Execution
- Product Security
- Automated Infrastructure
- Application Vulnerability Management
- Thread Modelling
Collect, analyse, infer, and present data across five maturity stages using a four-phased process. The proficient DevOps environment at Revolux enhances system agility, sustains speed, and nurtures innovation.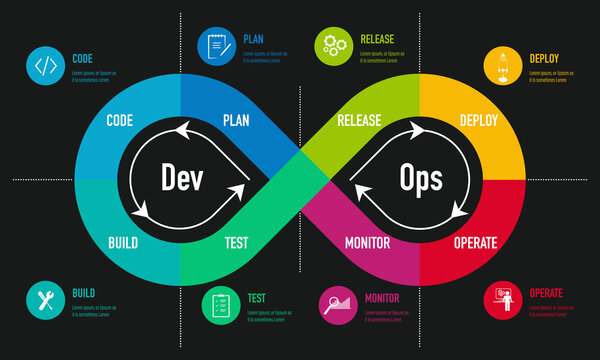
Develop products with a security-centric approach to ensure secure data management, enforce access control, and mitigate damages, adhering to container and micro services security principles. Utilising our Jira plugin, the DevOps framework enables comprehensive traceability of security defects and seamlessly integrates security testing into your continuous integration system.
Enhance infrastructure agility though process modularisation and utilise DevOps configuration management. We design optimised CI/CD pipelines that incorporate security at every stage, starting from the IDE, through base images, to application security testing.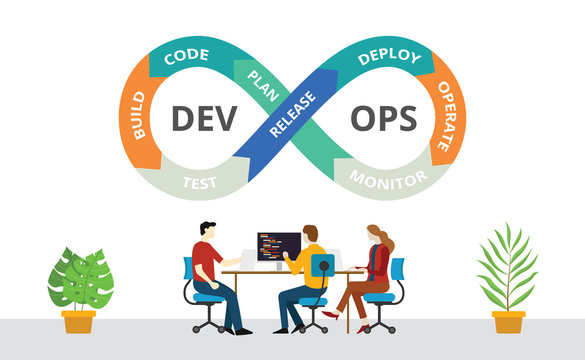
Support automated risk and vulnerability assessment, correlating all vulnerabilities, deduplication, and identifying false positives, among other specialized risk and vulnerability assessment techniques.
Examine the threat landscape and integrate security during the design phase. We identify threats through methodologies such as STRIDE, VAST, or PASTA, and use the DREAD model to assess severity, seamlessly integrating threat modeling into the development cycle.